Iran's Cyber Operations and the Chinese Infrastructure Underneath It
A wide range of threat groups are executing Iran's cyber retaliation after Operation Epic Fury, with Chinese technology quietly underpinning part of the offensive architecture.
The United States and Israel launched Operation Epic Fury on February 28, 2026, striking Iranian regime leadership structures, military installations, and nuclear-related sites across the country.
What followed in the cyber domain was not improvised. Palo Alto Networks’ Unit 42 says some estimates put the number at roughly 60 active groups, including pro-Iranian and pro-Russian actors. Understanding the scope of that retaliation requires understanding who built part of the foundation underneath it.
China’s Enabling Role in Iran’s Cyber Infrastructure
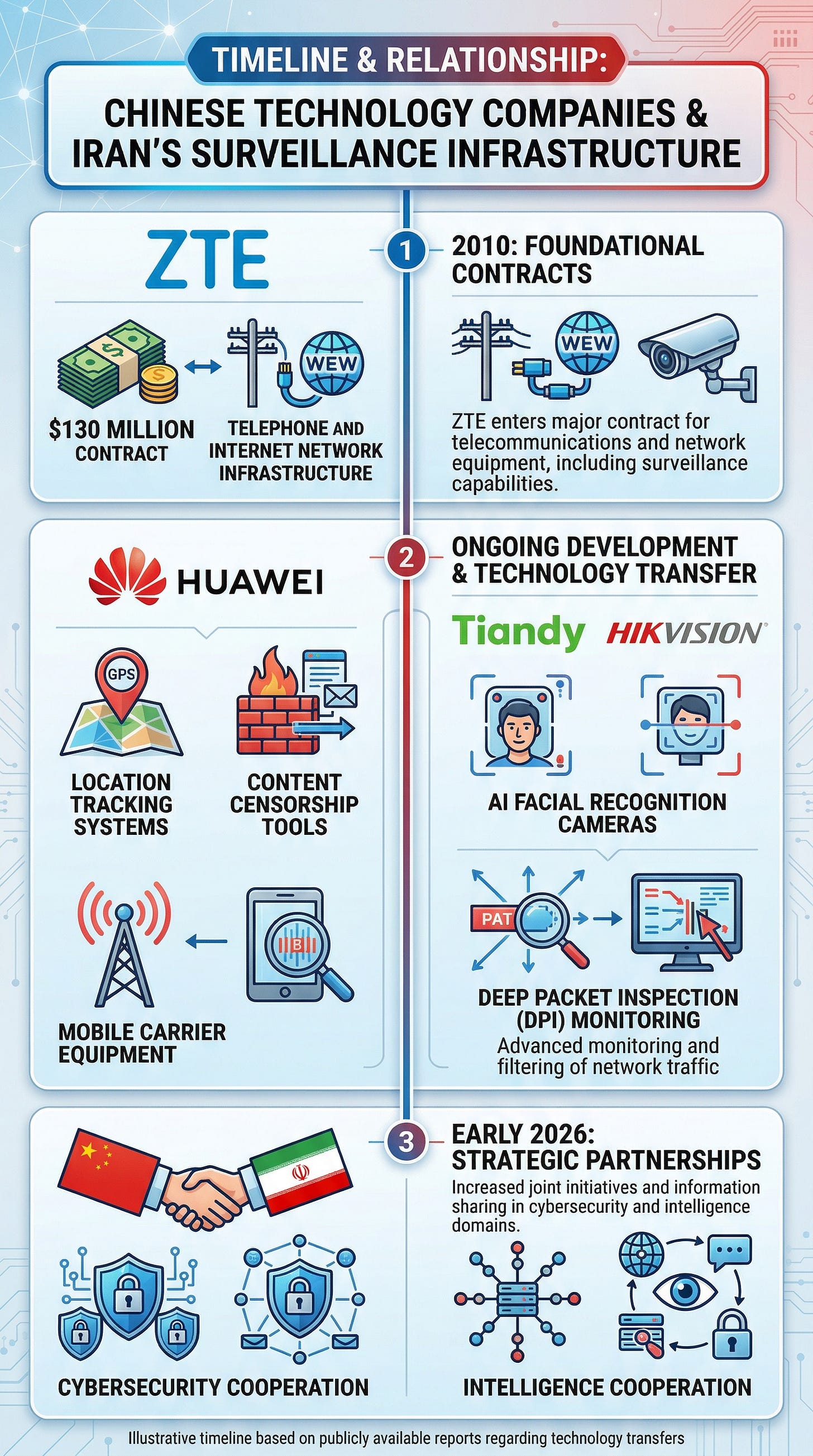
Chinese telecoms giants Huawei and ZTE helped build and equip important parts of Iran’s core digital backbone. In 2010, ZTE signed a $130 million contract to overlay a surveillance system onto Iran’s state-managed telephone and internet networks.
Huawei became a major telecom equipment supplier in Iran, supplying location-tracking services and content-censorship tools to mobile carriers. Chinese firms Tiandy and Hikvision subsequently supplied AI-enabled facial recognition cameras, while ZTE and Huawei provided DPI and related monitoring tools that enabled extensive surveillance and filtering across major parts of Iran’s telecom infrastructure.
In early 2026, Beijing deepened that integration further. According to Defense Mirror, citing the Russian Arms Telegram channel, eported that a new China-Iran cooperation package could expand cyber and intelligence coordination and support Iran’s shift toward wider use of BeiDou.
Shanghai-based firm MizarVision has been publicly posting detailed satellite imagery of U.S. military movements — aircraft types, numbers, and positions across Israel, Saudi Arabia, and Qatar — throughout Operation Epic Fury.
Analysts cited by the South China Morning Post said the disclosures underscored Beijing’s intelligence reach. The imagery was released publicly, in granular detail, during active U.S. military operations against one of China’s most strategically valuable Middle Eastern partner.
The Article 19 report published in February 2026 documented how ZTE, Huawei, Tiandy, and Hikvision continued operating in Iran through third-party intermediaries despite international sanctions.
The Cyber Retaliation in Action
Iran’s domestic internet connectivity dropped to 4 percent of normal levels in the hours following the initial strikes, the result of both kinetic infrastructure damage and deliberate network shutdowns.
Palo Alto Networks’ Unit 42 assesses that this collapse significantly constrains sophisticated, centrally coordinated cyberattacks originating from within Iran in the near term. State-aligned cyber units are likely operating in tactical isolation, introducing unpredictability while limiting precision. The offensive weight is therefore being carried by Iran-aligned entities operating outside the country, several of which have coalesced under an “Electronic Operations Room” formally stood up on February 28, 2026.
Key groups documented by Unit 42 include:
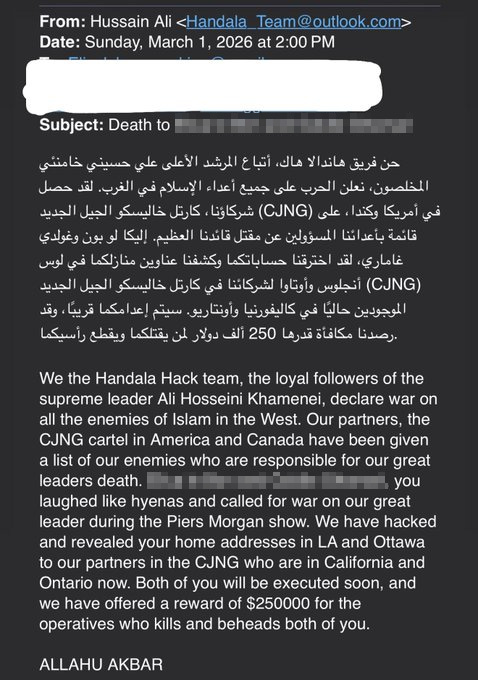
Handala Hack, assessed as linked to Iran’s Ministry of Intelligence and Security (MOIS), claimed responsibility for breaching an Israeli energy exploration company, compromising Jordan’s fuel systems, and targeting Israeli civilian healthcare. In a significant escalation, the group also emailed death threats to Iranian-American and Iranian-Canadian influencers, claiming to have passed their home addresses to physical operatives in North America.
The FAD Team (Fatimiyoun Cyber Team) claimed unauthorized access to multiple SCADA and PLC industrial control systems in Israel and over 24 systems belonging to an Israeli private security firm. The Cyber Islamic Resistance, coordinating groups including RipperSec and Cyb3rDrag0nzz, claimed to have compromised a drone defense and detection system and Israeli payment infrastructure. DieNet claimed DDoS attacks on airports in Bahrain and the UAE and targeted the Bank of Jordan. 313 Team, based in Iraq, claimed hits on Kuwait’s Armed Forces, Ministry of Defense, and government websites.
Pro-Russian hacktivist groups have joined the campaign in parallel. The group “Russian Legion” claimed access to Israel’s Iron Dome missile defense system. NoName057(16) claimed disruptive operations against a range of Israeli municipal, telecom, and defense entities. The ransomware group Tarnished Scorpius (INC Ransomware) listed an Israeli industrial company on its leak site and replaced its logo with a swastika.
What Dismantling Iran Means for Beijing
Iran's cyber retaliation after Operation Epic Fury is primarily the product of Tehran's own two-decade investment in state-sponsored APT capabilities, hacktivist proxy networks, and geographically dispersed operational cells. But Chinese technology has played a meaningful supporting role, embedding itself into Iran's telecommunications backbone, surveillance architecture, and navigation systems in ways that reinforce regime resilience and operational capacity.
Degrading Iran's command structures and communications infrastructure through continued kinetic operations will inevitably erode some of that Chinese-built foundation alongside it.




This is the key. You have pegged it. Why others don't see is beyond me. Thank you Jewish Onliner, restacking.